The HackRF Guide Nobody Asked For
Why this tiny device is both fascinating and terrifying
What Even is a HackRF?
Picture this: It’s a tiny USB device that costs less than your monthly coffee budget but can mess with radio signals from 1MHz to 6GHz. That’s basically everything from AM radio to WiFi, Bluetooth, and your neighbor’s baby monitor.
The device features a maximum transmission power of 30mW and connects via USB to provide up to 20 million samples per second. While this transmission power is relatively low, it’s sufficient for close-range experimentation and testing. The device is compatible with GNU Radio software, allowing integration with various other tools and protocols.
A Brief History Lesson
Back in 2012, Michael Ossmann had a brilliant idea: “What if we made radio hacking accessible to broke college students and curious degenerates?” Thus, HackRF was born.
The timeline:
2012: Michael Ossmann introduces the concept of an affordable, open-source SDR
2013: Successful Kickstarter campaign launches mass production
Present: HackRF becomes the go-to SDR device for researchers and enthusiasts worldwide
Which HackRF Is That?
HackRF Jawbreaker
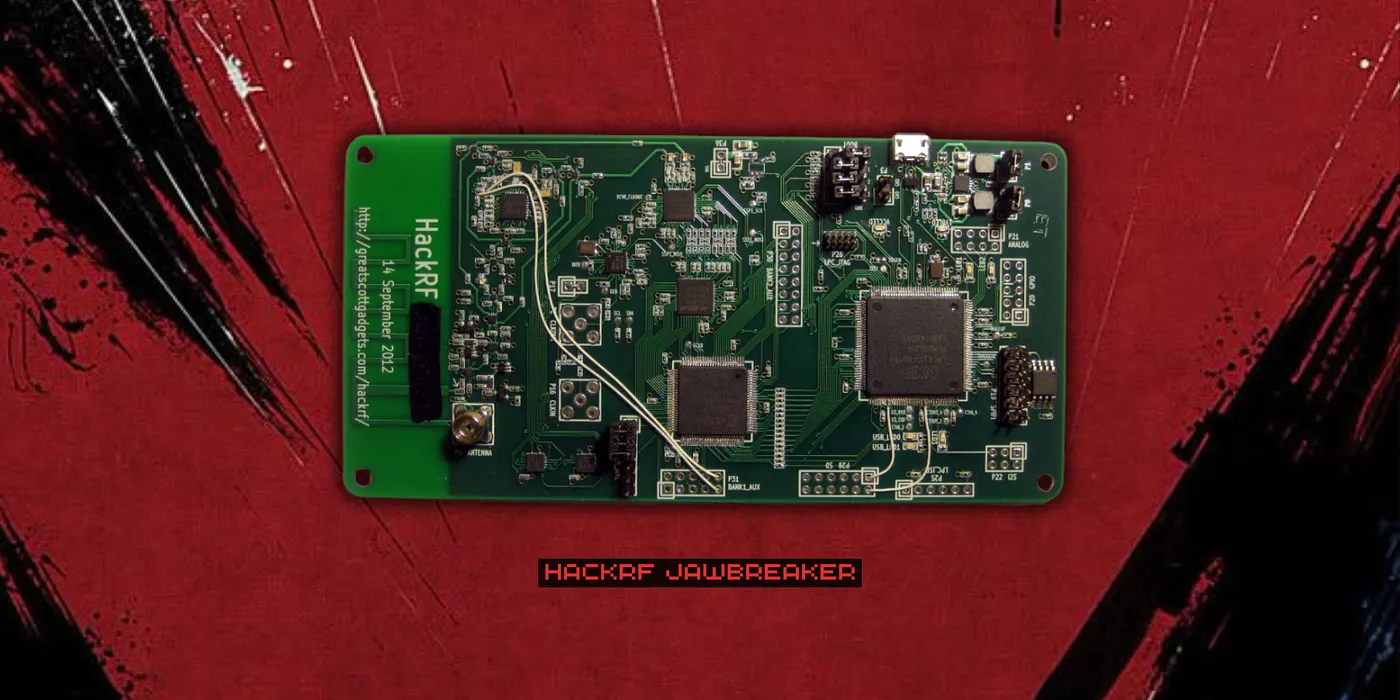
HackRF Jawbreaker marked the beginning of the project in 2012–2013, serving as the initial prototype with a limited production run of approximately 500 units that proved the concept’s viability.
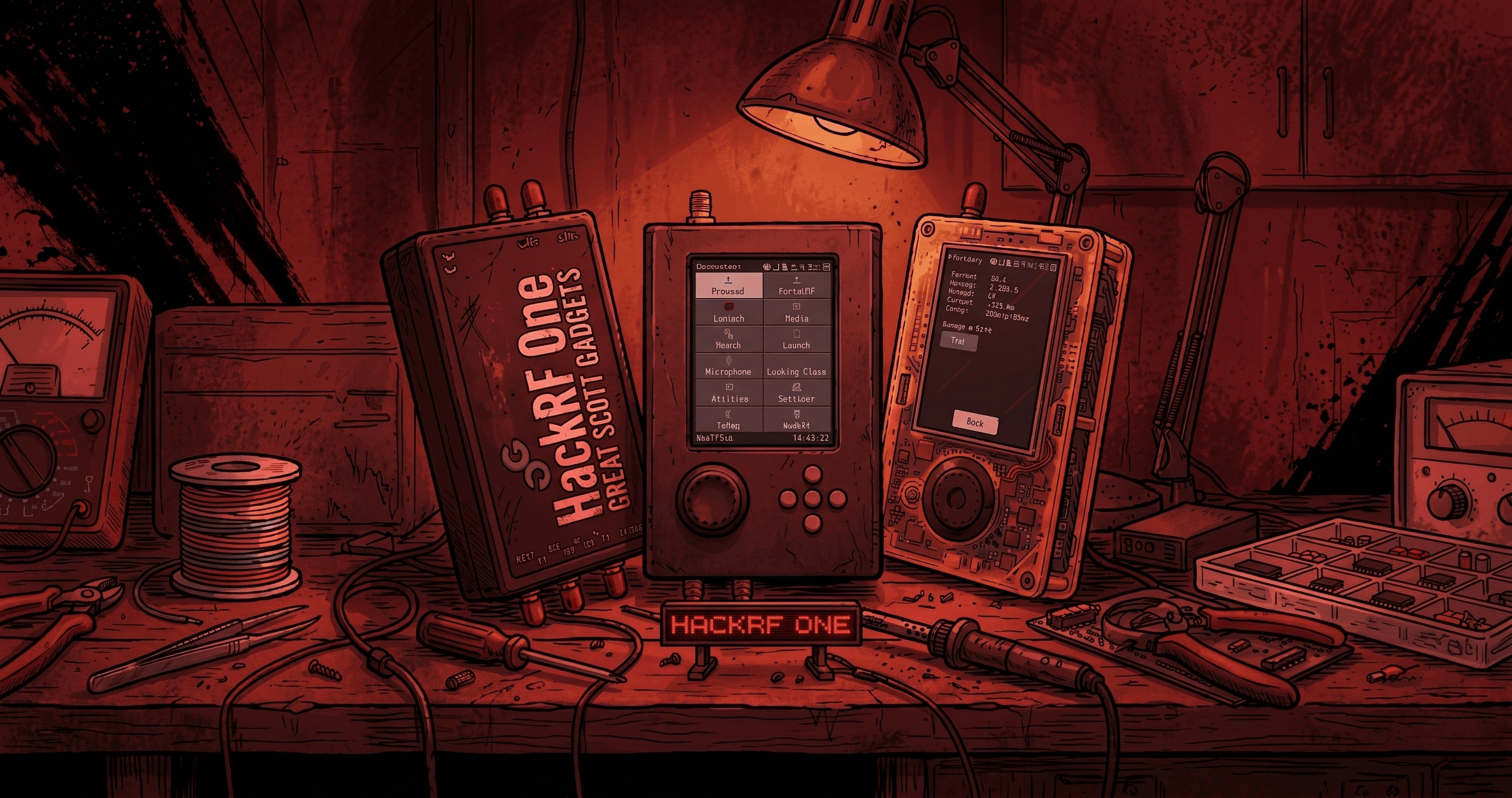
HackRF One

The HackRF One, introduced in 2013, became the main production version and continues to be manufactured today, featuring significant improvements over the Jawbreaker design and establishing itself as the standard model.
HackRF One + PortaPack H1

The HackRF One with PortaPack H1 transformed the basic HackRF One by adding a display module that enabled standalone operation without a computer, featuring an LCD touchscreen interface and built-in battery support for portable use.
HackRF One + PortaPack H2
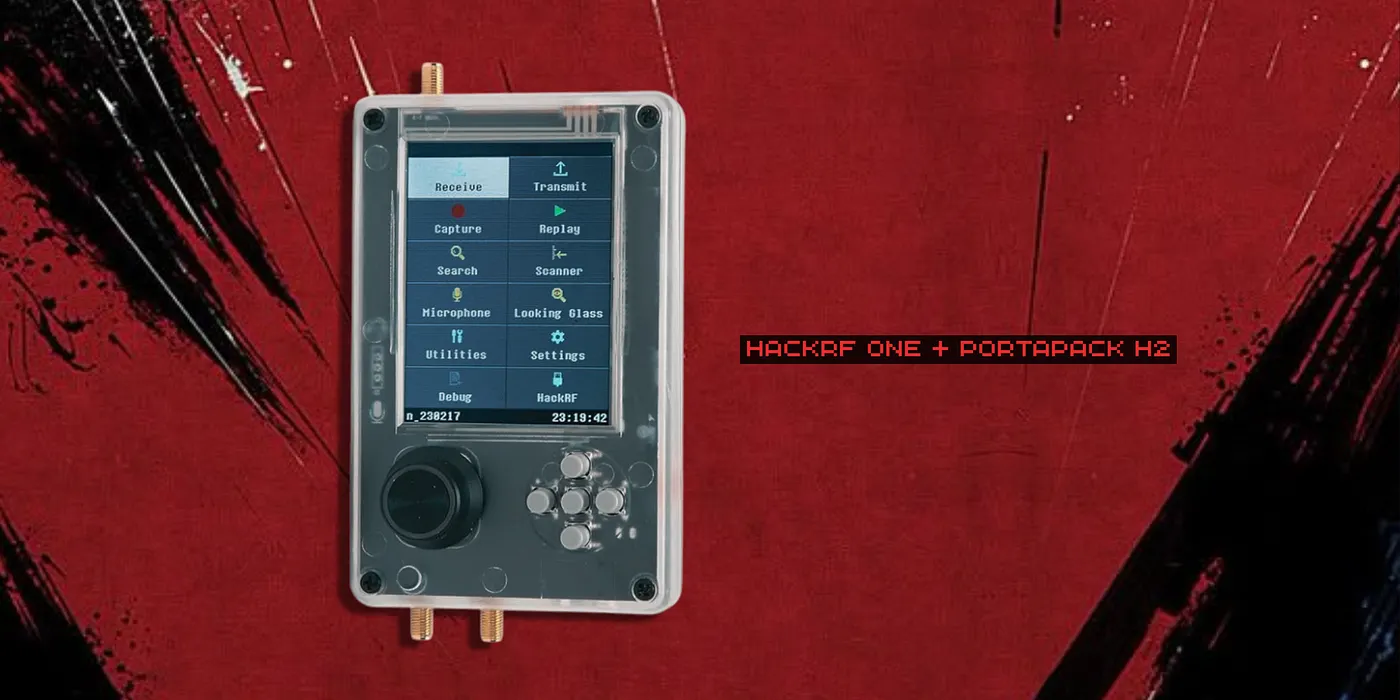
The HackRF One with PortaPack H2 represents the latest evolution, building upon the H1’s foundation with an improved display, enhanced interface, and more capable firmware to deliver a more refined user experience.
The Fun Stuff aka “Educational Purposes Only”
RF Jamming
Want to make WiFi disappear faster than your motivation on Monday morning? RF jamming works by transmitting disruptive signals at the same frequency as your target, essentially drowning out legitimate communications.
Common jamming techniques include:
Spot Jamming: Targeting a specific frequency
Barrage Jamming: Affecting multiple frequencies simultaneously
Sweep Jamming: Moving across a range of frequencies
Replay Attacks: Ctrl+C, Ctrl+V for RF
This is probably the most straightforward attack in the RF world:
This attacks involve capturing and retransmitting radio signals to gain unauthorized access or trigger unintended actions. This attack vector exploits systems that lack proper authentication mechanisms.
The process involves:
Intercepting the original signal
Recording the transmission
Replaying the signal at a chosen time
Achieving the same result as the original transmission
GSM Hacking: Pretending to be a Cell Tower
IMSI (International Mobile Subscriber Identity) catchers are devices that mimic cellular base stations to intercept mobile communications. These tools demonstrate vulnerabilities in cellular network protocols.
IMSI catchers work by broadcasting stronger signals than legitimate cell towers, causing nearby mobile devices to connect automatically. Once connected, they can intercept communications and track device locations.
GPS Spoofing: “You Are Here” But Not Really
Why settle for being where you actually are when you can convince your GPS you’re literally anywhere else? GPS spoofing transmits fake GPS signals that override the real ones, making your GPS receiver calculate a completely false location.
Unlike GPS jamming which just blocks signals, spoofing is more sophisticated and harder to detect. Your navigation system thinks everything is normal while being completely wrong about where you are.
Side-Channel Analysis
Here’s where things get really creepy. You can literally watch someone’s monitor through radio waves. HDMI cables leak RF signals that correspond to what’s being displayed on screen, and with the right setup, you can recreate what someone is looking at on their computer.
This technique demonstrates how electronic devices can leak information through electromagnetic signatures, emphasizing the importance of proper shielding and security measures.
Essential Software Tools
Recommended Applications:
SDR++ : Comprehensive SDR software with spectrum analysis capabilities
hackrf-spectrum-analyzer : Specialized tool for RF spectrum visualization
qSpectrumAnalyzer : Cross-platform spectrum analysis application
Final Thoughts
The HackRF is a gateway drug to the world of RF security. One day you’re just curious about how WiFi works, the next day you’re explaining to airport security why you have a USB device that can “theoretically” interfere with aircraft navigation systems.
For less than $300, you get a device that can explore most of the radio spectrum. Compare that to traditional test equipment costing tens of thousands of dollars, and you understand why this little USB stick revolutionized the RF world.
Resources to Dive Deeper
GitHub — Introduction to HackRF
Great Scott Gadgets — Official HackRF site
GNU Radio — The foundation of SDR
RTL-SDR Blog — Stay updated with SDR news
Kickstarter Campaign — The campaign that started it all
Not Gonna Lie, This Part Matters
Most countries have strict regulations about RF transmissions, and jamming GPS or cellular signals can land you with massive fines or prison time. I’m not legally responsible if you end up jamming satellites play with RF at your own risk.